What's New
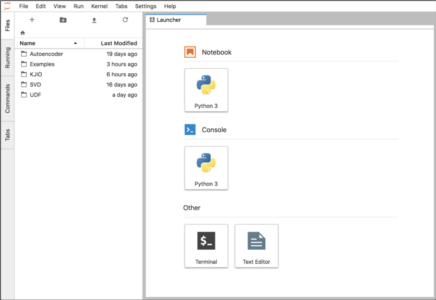
Go to:Introduction JupyterLab is an integrated environment that can streamline the development of Python code and Machine Learning (ML) models in Kinetica. With it you can edit Jupyter notebooks that integrate code execution, debugging, documentation, and visualization in a single document that can be consumed by multiple audiences. The development process is streamlined because sections of…
When you’ve got a large amount of files, like images, in a folder on your cluster where Kinetica’s running, you might want to access that data through the Kinetica database. With the Kinetica File System (KiFS) there’s no need for ingest! You can mount that directory to Kinetica and the files will automatically be mirrored…
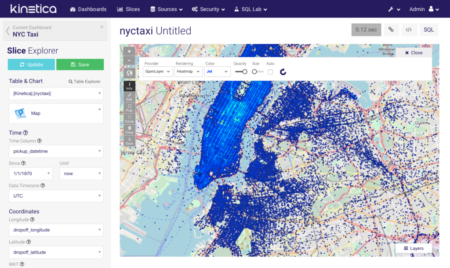
While Big Data analytics has been around for many years now, one of the most tedious and challenging processes is loading your data into a system, creating relevant charts and/or maps in a dashboard, and performing interactive analysis by applying filters to your data. Kinetica provides all the easy-to-use tools you need to load and…
In 1882, the invention of the electrical grid transformed our lives forever. Dramatic strides in health, efficiency, productivity, and more followed the expansion of electricity across the globe. However, little has changed about the grid in more than a century. For decades, we have been promised the next evolution in the form of the connected…
What’s the most powerful tool government has to improve the lives of its citizens? Data, hands down. Data delivers an unprecedented opportunity to positively impact the citizen’s day-to-day life. Government has nearly infinite resources, and with the right analytics tools and platforms, it can use data to revolutionize citizen services and safety. Its uses can…